How Multi-Persona IAM Secures Access Without Slowing Teams Down
As modern identity and access management (IAM) grows increasingly complex, it introduces new challenges for organizations.
Today, one person doesn’t just have a single account. They wear multiple hats throughout the day: a user might log in as an employee in the morning, approve budgets as a manager at noon, and troubleshoot systems as an admin later that day. While traditional IAM wasn’t built for that, multi-persona IAM is.
Keep reading to learn what multi-persona IAM is, why it matters, and how organizations leverage it without added friction.
Why Over-Permissioning Became the Default
Traditional IAM systems were built on a simple idea: one person = one account. This model was successful until the environment grew more complex. Today, people operate across multiple systems, roles, and contexts:
- Employees interact with internal systems, partner platforms, and customer portals
- IT staff operate as both standard users and privileged administrators
- Developers act as coders, DevOps engineers, or CI/CD pipeline managers
- External users function as both customers and business partners
Legacy IAM systems are not equipped to handle these use cases. To keep up, many organizations take shortcuts by creating multiple accounts for the same user, leading to:
- Overly complex role definitions
- Excessive privileges “just in case”
- Poor visibility into who performed what action
The result is over-permissioning, an increased risk of identity-based attacks, privilege misuse, and compliance failures. Additionally, they limit the mechanisms in which an identity can interact with the organization’s systems.
Multi-persona IAM provides a solution by separating who someone is from what they’re doing in the moment.
A Simple Example to Make it Click
Imagine Bob in finance is on your team. When Bob:
- Checks Payroll: He’s acting as an employee
- Approves Budgets: He’s operating as a manager
- Helps Test a System: He’s temporarily an admin
In this example, Bob is acting as a single person in different contexts that require different levels of access.
Instead of giving Bob broad access to everything all the time, multi-persona IAM adjusts his access based on what he’s doing depending on the context. This is how you reduce risk without slowing him down.
Understanding the Basics (Identities, Accounts, Roles, and Personas)
- Identity: The person or system (non-human)
- Account: Their login
- Role: What they are allowed to do
- Persona: The context they are operating in (e.g., multiple roles, authentication requirements, authorization boundaries, compliance constraints, and monitoring or logging policies)
Rather than creating multiple accounts for each use case, multi-persona IAM allows one identity to switch between personas depending on the situation.
The 3 Things That Make Multi-Persona IAM Work
1. Persona Activation: What Are You Doing Right Now?
Persona activation determines which “mode” a user is operating during a session. Instead of assigning static access, multi-persona IAM systems evaluate context in real time:
- Who needs access? (human or non-human)
- What task is being performed?
- What role is required? Are there any risk signals?
- Is this a normal or elevated action?
Real-world examples include:
| Scenario | Activated Persona |
|---|---|
| Employee checking HR portal | Employee |
| Same employee managing infrastructure | Administrator |
| Developer deploying code | DevOps |
| External user | Customer |
Persona activation can be either dynamic or explicit: dynamic activation evaluates context automatically at the time of access while explicit activation, typically for higher-risk actions, requires deliberate user intervention. This adds an extra layer of control and visibility of high-risk actions in audit records.
2. Policy Enforcement by Persona: Access Changes with Context
In multi-persona IAM, access policies are tied to the active persona and not the account. This reduces over-permissioning.
Each persona defines:
- Authorization Boundaries: What can be accessed / what actions are allowed
- Authentication Requirements: What level of authentication is required (e.g., ID and password, MFA, and adaptive authentication)
- Identity Assurance: The level of confidence that an identity is who (or what) it claims to be at the time a persona is activated and used
- Risk and Compliance Constraints: What compliance rules apply
When the persona changes, the enforcement conditions or rules change in real time. This ends the mindset of “just give them access to everything so they don’t get blocked.”
3. Identity Data Fabric: The Layer That Makes it all Work
An Identity Data Fabric works behind the scenes to provide the data layer required to support multi-persona IAM.
It consolidates fragmented identity data from authoritative sources for a unified identity profile used to evaluate persona context at runtime. These sources include:
- HR systems
- Corporate directories
- SaaS applications
- Customer databases
- Partner platforms
- Privileged access management tools
- DevOps systems
An Identity Data Fabric performs several core functions:
| Function | Description |
|---|---|
| Identity Correlation | Links identity records across systems using matching logic to establish a unified identity and reduce duplication. |
| Attribute Normalization | Standardizes identity attributes across disparate systems, so policies can be evaluated against a consistent data model. |
| Computed Attributes | Derives attributes using business logic to support context-aware decisions that are not directly available from authoritative sources. |
| Real-time Updated and Improved Performance | Using caching and optimized retrieval to support low-latency access decisions based on current identity data. |
The identity data fabric creates a consistent view of each identity, ensuring no duplicate users, no conflicting data, and real-time decisions based on accurate information. It’s what allows IAM systems to evaluate context and enforce the right persona instantly.
Architecting a Multi-Persona IAM Model
Reference Architecture
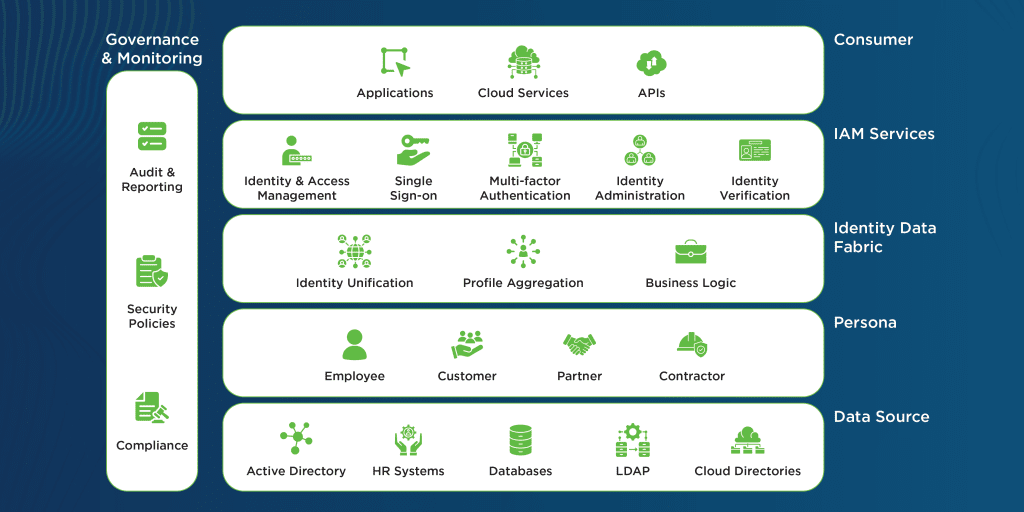
The following diagram outlines the multi-persona IAM reference architecture:
Architecture Flow
Personas are implemented within the IAM reference architecture as follows:
- Identity and Attribute Data Source Layer: The various human and non-human identities contained within the authoritative data sources across the environment.
- Persona Layer: The mapping of identity data that defines the determined personas. Examples of a persona include an identity that operates as an employee, customer, partner, or contractor. A user could be part of a single persona or multiple personas.
- Identity Data Fabric Layer: The cached layer where identity and attribute data is unified into a single common identity, attributes are standardized to a common set of values, and business logic is applied to generate computed attributes or define attribute priority.
- IAM Services Layer: IAM services deliver core security and user management functionality mapped to the defined personas. The persona maps the authenticated user’s session to what the identity is allowed to do and under what conditions. Roles can be defined based upon the personas associated with the identity, allowing user management and resource authorization.
- Governance and Monitoring Layer: Governance and monitoring apply to all the IAM layers. This layer enforces adherence to compliance guidelines, provides traceability for each layer, and delivers non-repudiation for an identity based upon its active persona.
- Consumer Layer: The various clients of the IAM systems services and identity data. This includes applications, APIs, and cloud services.
This framework delivers the core infrastructure required for delivering multi-persona IAM to an organization.
Implementing a Multi-Persona Identity Data Fabric: How it all Comes Together
At a high level, the implementation process is defined by creating a unified identity, defining personas based on context, and establishing robust governance:
- A Unified Identity is Created: Implementing a multi-persona identity data fabric starts with designing a unified identity layer that can represent a single individual across multiple contexts without duplicating profile data. This is done by creating an identity model that links disparate user attributes using a unique identifier.
- Personas are Defined Based on Context: The model must ensure that persona-specific attributes and entitlements are maintained when creating the unified identity layer. Profile data from directories, HR systems, application databases, CRM systems, and cloud-based systems should be consolidated into an Identity Data Fabric through normalization and schema mapping. This ensures that identities are represented by a common framework. A profile attribute-based architecture enables relationships between identities, roles, devices, and sessions. This identity data can also be dynamically queried for identity and security systems.
- Data and Process Governance is Established: Robust governance is required to maintain clear ownership of attributes, capture mappings between authoritative sources, define required business logic, and implement privacy controls. This ensures that the appropriate persona data is provided for the context in which the identity is operating. This also enables least-privilege access by delivering only the profile data necessary for the operations performed.
Six Best Practices for a Successful Implementation: What it Takes to get this Right
Once the foundational layer is defined, a few things separate successful implementations from the rest:
- Policy-Driven Access: A policy-driven architecture that dynamically determines which persona is active and what access should be granted.
- Strong Integration: Deployment and integration between authentication, single sign-on (SSO), identity verification, and MFA systems to enable security decisions based on persona selection.
- Risk-Based Authentication: Risk-based step-up authentication based upon real-time delivered profile attributes.
- Real-Time Data Synchronization: Event-based synchronization or provisioning leveraged to propagate identity attributes, ensuring that security data is consistent when a user switches roles or attributes are updated.
- Clear Visibility and Auditability: Identity observability features such as identity graphs, audit data, and persona-level monitoring.
- Seamless User Experience: End-user experience prioritizing minimal friction for seamless persona switching. This must be balanced with controls that ensure each persona is enforced independently based on its defined access and control conditions.
Contextual Persona-Based Identity is the Future of IAM: The Real Payoff
Multi-persona IAM moves beyond a technical upgrade, shifting how teams think about access.
As organizations bring together workforce, customer identity, partner access, identity verification, and privileged access management, IAM systems must support the increasing complexity of user personas. Multi-persona IAM-based architectures provide a scalable framework for managing this complexity. Done right, it helps:
- Reduce over-permissioning and risk
- Improve audit readiness and compliance
- Simplify identity management
- Enable your teams to move faster without friction
People don’t work in a single context, and IAM shouldn’t treat them that way in modern identity systems. Multi-persona IAM provides secure access based on real-world behavior, not static assumptions. It offers a solution to exit the cycle of over-permissioning, without slowing down teams and critical business operations.