The cybersecurity domain is witnessing a new wave of transformation akin to the early 2000s/SOX era, once again driven by…
As we step into the next chapter of technological evolution, the role of cloud computing continues to expand and redefine…
Choosing Your Cybersecurity Team: A Surgical Approach to Selecting a SASE Provider The Art of Surgically Precise Cybersecurity In the…
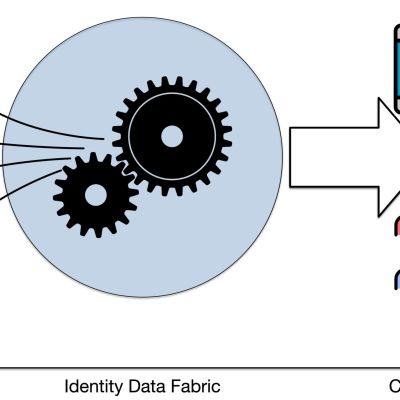
The sprawl of information across multiple repositories has complicated managing identity data. The addition of an Identity Data Fabric enables…
The healthcare sector is ensnared in a relentless vortex of risk and regulation amid unanticipated disruptions and transformations. Navigating through…
Vishing, a blend of voice and phishing attacks that traditionally targeted consumers to compromise their financial accounts, is now an…
Development, Security, and Operations (DevSecOps) enablement is the process of integrating security practices into the Development and Operations (DevOps) workflow….
Enterprises across the globe are fast-pacing zero trust initiatives as compliance regulations stiffen, government mandates are enforced, and advanced cyberattacks…
This article will cover integrating an Identity Data Fabric with AI to gather insights into your user data. Additionally, it…
Navigating Business Transformation with Intelligent Automation Enterprises across the globe are facing fast-paced business transformations, and the COVID-19 pandemic has…